Front view woman wearing trucker hat.
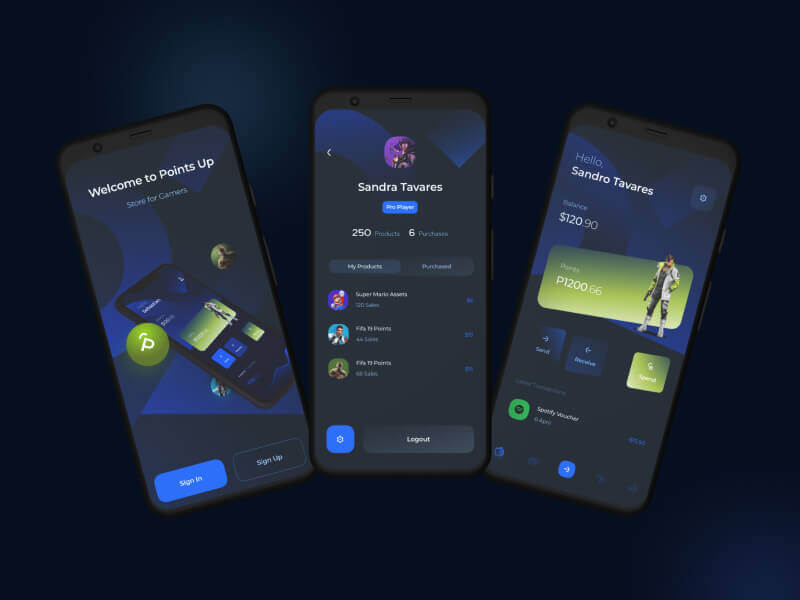
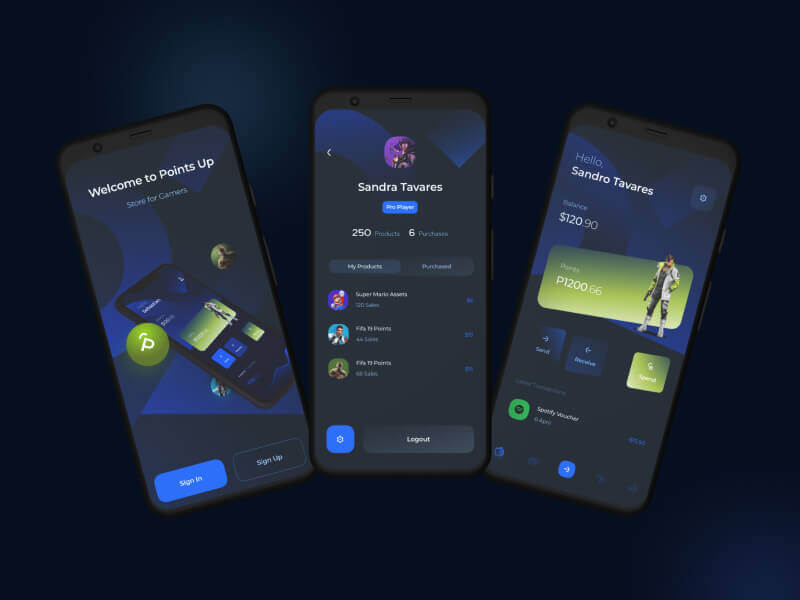
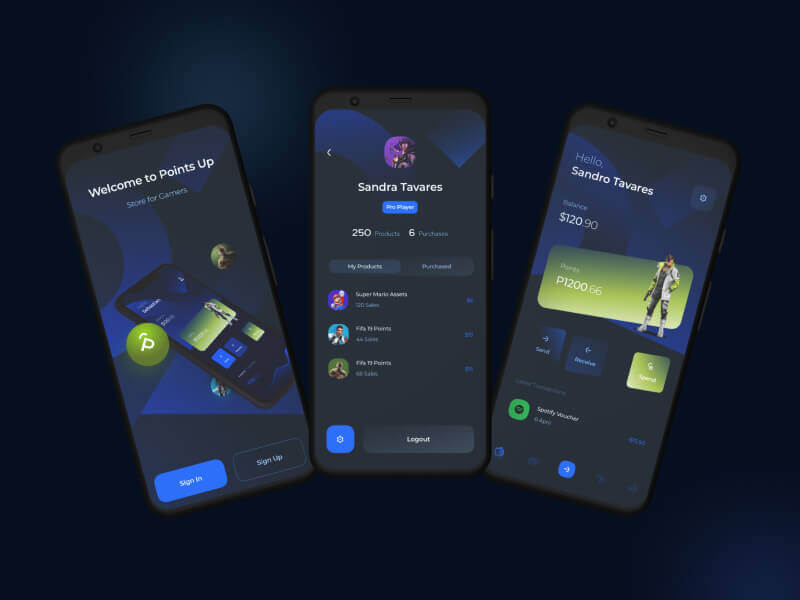
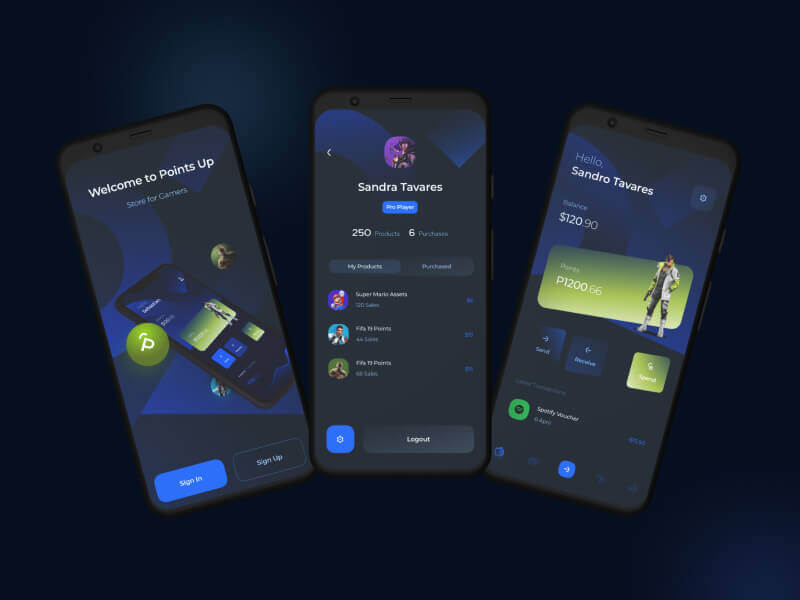
Through a wide variety of mobile applications
- Client Nusrat Nill
- Date 25 June 2021

Lorem ipsum dolor sit amet, consectetur adipisicing elit. Eum in eos saepe ipsa cupiditate accusantium voluptatibus quidem nam, reprehenderit, et necessitatibus adipisci.
Lorem ipsum, dolor sit amet consectetur adipisicing elit. Inventore dolorum atque dicta distinctio mollitia fuga.
Lorem ipsum, dolor sit amet consectetur adipisicing elit. Inventore dolorum atque dicta distinctio mollitia fuga.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
Contrary to popular belief. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
Generate Lorem Ipsum which looks. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
Contrary to popular belief. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
Generate Lorem Ipsum which looks. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
Maecenas finibus nec sem ut imperdiet. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
Through a wide variety of mobile applications

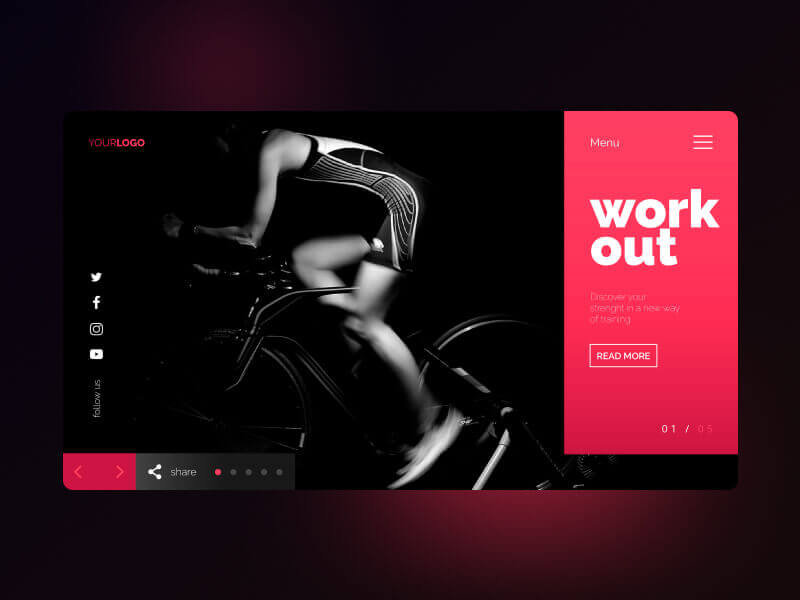
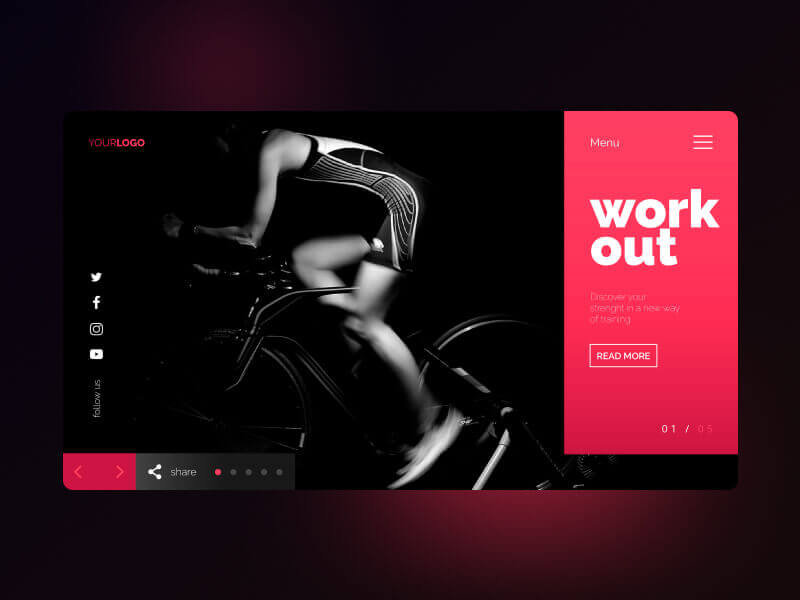
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.
However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria
Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
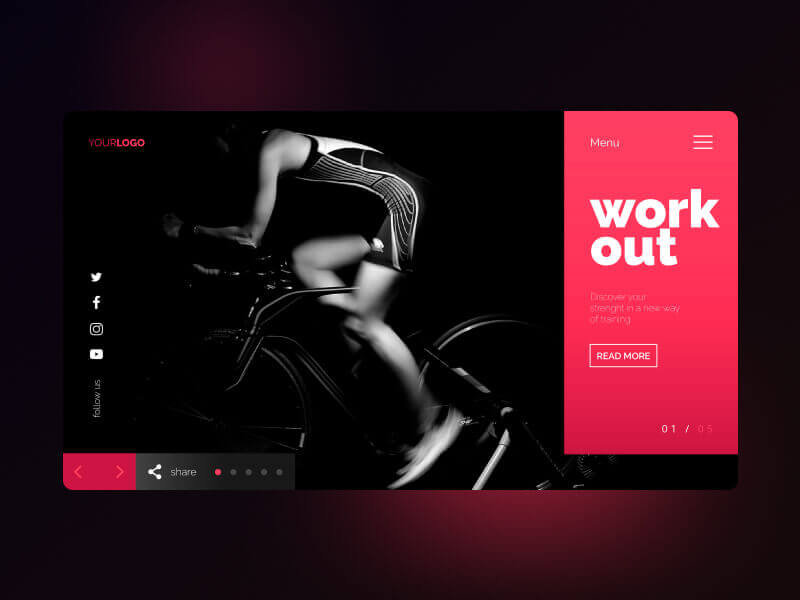
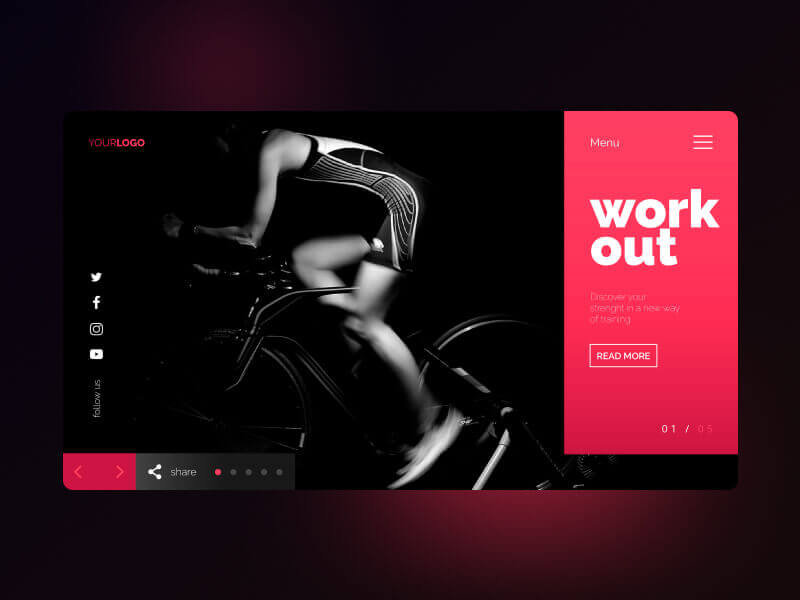
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.
There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.
Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.

However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria

Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them.
Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria

Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.
There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.
Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.

However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria

Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.
There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.
Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.

However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria

Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.
There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.
Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.

However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria


This course teaches IT Professionals how to manage their Azure subscriptions, secure identities, administer the infrastructure, configure virtual networking, connect Azure and on-premises sites, manage network traffic, implement storage solutions, create and scale virtual machines, implement web apps and containers, back up and share data, and monitor your solution.
Module 1: Identity
In this module, you will learn how to secure identities with Azure Active Directory, and implement users and groups.
Lab : Manage Azure Active Directory Identities
After completing this module, students will be able to:
Module 2: Governance and Compliance
In this module, you will learn about managing your subscriptions and accounts, implementing Azure policies, and using Role-Based Access Control.
After completing this module, students will be able to:
Module 3: Azure Administration
In this module, you will learn about the tools an Azure Administrator uses to manage their infrastructure. This includes the Azure Portal, Cloud Shell, Azure PowerShell, CLI, and Resource Manager Templates. This module includes:
After completing this module, students will be able to:
Module 4: Virtual Networking
In this module, you will learn about basic virtual networking concepts like virtual networks and subnetting, IP addressing, network security groups, Azure Firewall, and Azure DNS,
After completing this module, students will be able to:
Module 5: Intersite Connectivity
In this module, you will learn about intersite connectivity features including VNet Peering, Virtual Network Gateways, and Site-to-Site Connections.
After completing this module, students will be able to:
Module 6: Network Traffic Management
In this module, you will learn about network traffic strategies including network routing and service endpoints, Azure Load Balancer, Azure Application Gateway, and Traffic Manager.
After completing this module, students will be able to:
Module 7: Azure Storage
In this module, you will learn about basic storage features including storage accounts, blob storage, Azure files and File Sync, storage security, and storage tools.
After completing this module, students will be able to:
Module 8: Azure Virtual Machines
In this module, you will learn about Azure virtual machines including planning, creating, availability and extensions.
After completing this module, students will be able to:
Module 9: Serverless Computing
In this module, you will learn administer serverless computing features like Azure App Service, Azure Container Instances, and Kubernetes.
After completing this module, students will be able to:
Module 10: Data Protection
In this module, you will learn about backing up files and folders, and virtual machine backups.
After completing this module, students will be able to:
Module 11: Monitoring
In this module, you will learn about monitoring your Azure infrastructure including Azure Monitor, alerting, and log analytics.
After completing this module, students will be able to:
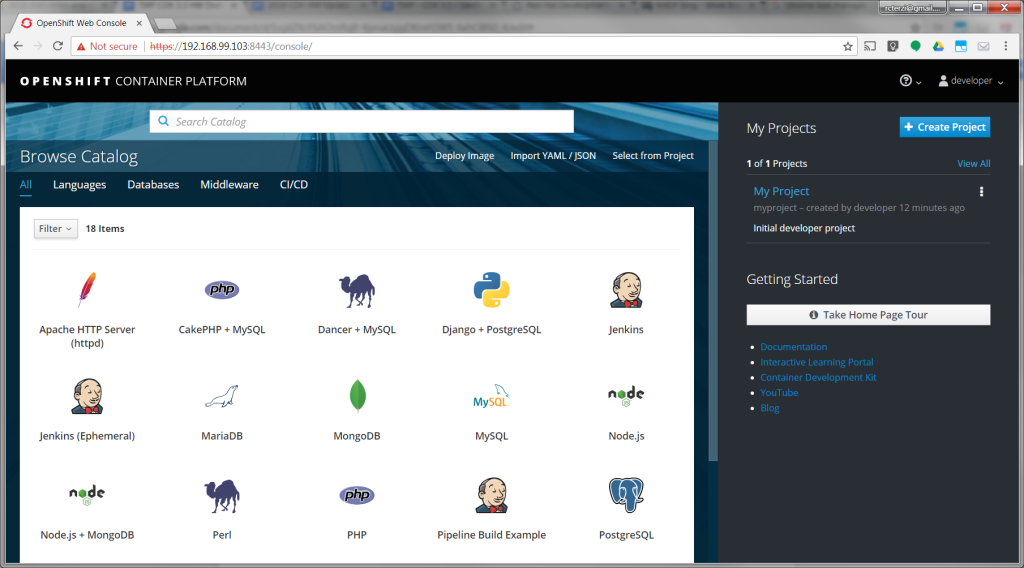
The following steps will guide you through creating your first project on Red Hat OpenShift Container Platform, which is running inside the Red Hat Container Development Kit on the minishift virtual machine. The project is a Node.js “Hello, World” application that displays the current hit count. A MongoDB database is used to store the hit count. Two pods will be created, one for the Node.js application and another for the database.
The source code for the project is available on GitHub: openshift/nodejs-ex. The OpenShift catalog in CDK has a number of project templates available including this sample Node.js application. For this guide, we will use the template from the OpenShift catalog. You will use the OpenShift web console to build and manage your application.
Note: This guide uses the OpenShift web console to build and manage your application. Alternatively you could use the oc CLI to accomplish the same steps. The following command would create the application pulling the source from GitHub:$ oc new-app https://github.com/openshift/nodejs-ex
For more information see Creating an Application using the CLI, in the Developer Guide section of the OpenShift documentation.
If you haven’t installed CDK, follow these instructions.
Start the CDK/minishift VM:$ minishift start
Once the VM is up and running, launch the web console in the browser:$ minishift console
Note: The web console may not launch on some older versions of Safari. You can get the URL to use with a different browser using the following command:$ minishift console –url
Log into the OpenShift console with developer as the username and any text for the password. A default empty project called My Project has been created for you. Alternatively, you can use the create project button to create a new empty project at any time.
Follow these steps to create, build, and deploy the application:
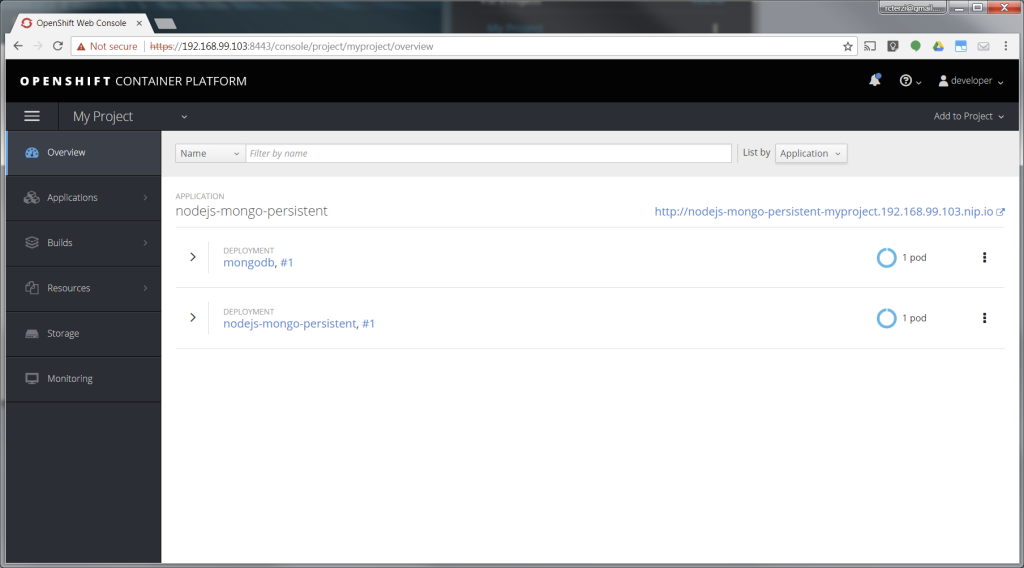
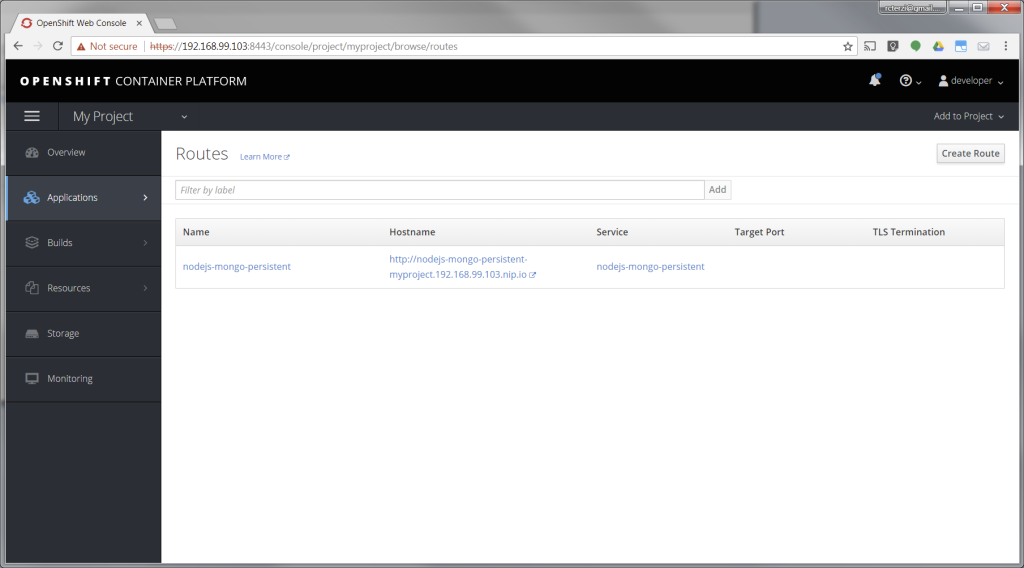
At this point, you’ve successfully built and deployed a Node.js and MongoDB application in containers running on OpenShift on your personal OpenShift cluster. Explore the menus to see the components that were created, view logs, and explore OpenShift.

2023

There are many variations of passages of Lorem Ipsum available, but the majority have suffered alteration in some form, by injected humour, or randomised words which don’t look even slightly believable. If you are going to use a passage of Lorem Ipsum. You need to be sure there isn’t anything embarrassing hidden in the middle of text. All the Lorem Ipsum generators on the Internet tend toitrrepeat predefined chunks.
The first of two courses covering the core system administration tasks needed to manage Red Hat Enterprise Linux servers
Red Hat System Administration I (RH124) is designed for IT professionals without previous Linux system administration experience. The course provides students with Linux administration competence by focusing on core administration tasks. This course also provides a foundation for students who plan to become full-time Linux system administrators by introducing key command-line concepts and enterprise-level tools.
This course is the first of a two-course series that takes a computer professional without Linux system administration knowledge to become a fully capable Linux administrator. These concepts are further developed in the follow-on course, Red Hat System Administration II (RH134).
This course is based on Red Hat® Enterprise Linux 9.0.
Following course completion, you will receive a 45-day extended access to hands-on labs for any course that includes a virtual environment.Note: This course is offered as a five day in person class, a five day virtual class or is self-paced. Durations may vary based on the delivery. For full course details, scheduling, and pricing, select your location then “get started” on the right hand menu.
Outline for this course
Get started with Red Hat Enterprise Linux
Describe and define open source, Linux, Linux distributions, and Red Hat Enterprise Linux
Access the command line
Log into a Linux system and run simple commands using the shell.
Manage files from the command line
Copy, move, create, delete, and organize files while working from the bash shell.
Get help in Red Hat Enterprise Linux
Resolve problems by using local help systems.
Create, view, and edit text files
Manage text files from command output or in a text editor.
Manage local users and groups
Create, manage, and delete local users and groups, as well as administer local password policies.
Control access to files
Set Linux file system permissions on files and interpret the security effects of different permission settings.
Monitor and manage Linux processes
Evaluate and control processes running on a Red Hat Enterprise Linux system.
Control services and daemons
Control and monitor network services and system daemons with the systemd service.
Configure and secure SSH
Configure secure command line service on remote systems, using OpenSSH.
Analyze and store logs
Locate and accurately interpret logs of system events for troubleshooting purposes.
Manage networking
Configure network interfaces and settings on Red Hat Enterprise Linux servers.
Install and update software packages
Download, install, update, and manage software packages from Red Hat and DNF package repositories.
Access Linux files systems
Access, inspect, and use existing file systems on storage attached to a Linux server.
Analyze servers and get support
Investigate and resolve issues in the web-based management interface, getting support from Red Hat to help solve problems.
Comprehensive review
Review the content covered in this course by completing hands-on exercises.


Cisco ACI is an enterprise-class, software-defined networking (SDN) solution that provides complete control of the data center network. Using a policy-based approach, Cisco ACI delivers security, performance, and scalability for today’s demanding applications.
Cisco ACI is part of the broader Cisco SDN portfolio, which also includes Nexus switches and Application Centric Infrastructure (ACI) controllers. If you are looking for a way to improve your data center network, Cisco ACI may be the answer. In this article, you can find out more about Cisco ACI, including how it works, its benefits, and what it is used for.
Cisco ACI is a software-defined networking (SDN) technology offering from Cisco that allows for centralized application policy enforcement across a data center network. It is designed to simplify and automate the creation, management, and enforcement of network security policies.
ACI provides uniform policy definition and application across physical and virtual resources, as well as bare-metal server deployments. This can be done through an easy-to-use graphical user interface or programmatically through APIs. The latter option makes it possible to integrate ACI into your existing DevOps processes.
With Cisco ACI, you can apply consistent security policies across your data center regardless of the underlying infrastructure. The result is increased agility and reduced operational costs. In addition, ACI provides built-in micro-segmentation capabilities that can help you improve your data center security posture.
Cisco ACI is based on the concept of an application profile. An application profile defines the set of network and security policies that should be applied to a particular application or workload. Application profiles are created using the Cisco Application Policy Infrastructure Controller (APIC).
The APIC is a centralized management system that gives you visibility into and control over the network resources in your data center. It also provides policy enforcement and orchestration capabilities. The APIC communicates with the network devices in your data center through an out-of-band management network.
Cisco ACI uses a leaf-spine architecture. The leaf nodes are Top-of-Rack (ToR) switches that connect to server endpoints. The spine nodes are core switches that connect the leaf nodes to each other.
Cisco ACI supports both physical and virtualized leaf nodes. Physical leaves can be either Cisco Nexus 9000 Series Switches or Cisco ASA 1000V Cloud Firewalls. Virtualized leaves are provided by the Cisco Avi Vantage platform.
SDN stands for software-defined networking. It’s a network architecture that uses programmable interfaces to enable more flexible and dynamic network control.
In traditional networks, the control plane is physically separate from the data plane. This means that the traffic flow is dictated by the hardware, which can be inflexible and difficult to change. In an SDN, the control plane is implemented in software, giving it more flexibility.
This separation of duties can make it easier to manage complex networks, because you can change the configuration of the network without having to physically reconfigure the devices. It also makes it possible to dynamically adjust traffic flow according to changing needs.
SDN controllers use protocols like OpenFlow to communicate with devices in the network. Using these protocols allows SDN to centrally control the flow of traffic, making it possible to implement policies that can optimize performance or reduce costs.
SDN is still a relatively new technology, and there are a number of different approaches to implementing it. But the basic idea is to use software to make networks more flexible and easier to manage.
In the most basic sense, ACI (Application Centric Infrastructure) is a data center network architecture that enables applications to be deployed and managed in a more flexible and efficient manner. ACI provides a single point of control for both physical and virtual networks, allowing for greater transparency and easier management of complex application environments.
ACI is designed to increase agility and efficiency in the data center by automating many of the tasks that have traditionally been manual or error-prone. For example, ACI can automatically provision new applications on the infrastructure, identify and correct errors in application configurations, and dynamically adapt network resources to changing application needs. By simplifying these tasks, ACI can help reduce deployment times and improve overall efficiency in the data center.
In addition to increasing agility and efficiency, ACI also provides improved security and compliance capabilities. ACI includes features such as built-in firewalls and intrusion detection/prevention systems, which can help protect data center assets from malicious attacks. ACI also provides granular visibility into application traffic, allowing administrators to quickly identify and respond to potential security threats.
Overall, ACI is a data center network architecture that enables applications to be deployed and managed in a more flexible and efficient manner. ACI can help improve agility, efficiency, security, and compliance in the data center.
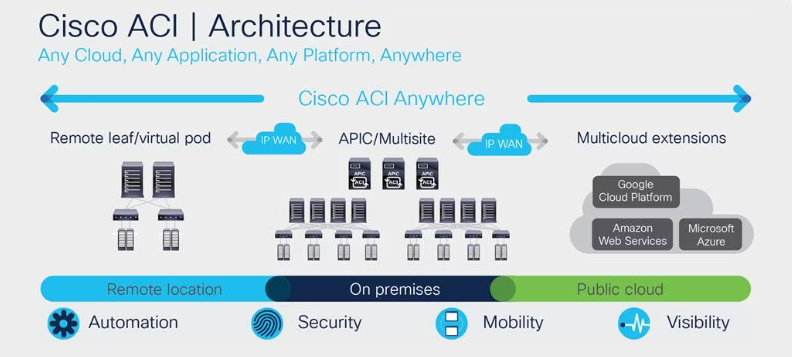
Cisco ACI is an application-centric infrastructure that enables you to build your data center network around the needs of your applications. ACI uses a centralized policy model to automate and simplify network configuration, deployment, and management. This architecture decouples the network control plane from the data forwarding plane, allowing for greater flexibility, scalability, and manageability.
ACI consists of three key components: the Application Policy Infrastructure Controller (APIC), the leaf switches, and the spine switches. The APIC is a centralized controller that manages all aspects of the ACI fabric. The leaf switches are ToR switches that provide connectivity between servers and external networks. The spine switches are aggregate Layer 3 switches that provide high-bandwidth connectivity between leaf switches.
The APIC provides a single point of control and management for the entire ACI fabric. It uses an open, standards-based application programming interface (API) to expose the ACI policy model to external applications and orchestration tools. The APIC also provides an intuitive web-based user interface (UI) for manual configuration and monitoring of the ACI fabric.
The leaf switches are ToR switches that provide connectivity between servers and external networks. Leaf switches are fully programmable and support all Layer 2 and Layer 3 protocols. In addition, leaf switches also support quality of service (QoS), security features, and virtualization capabilities.
The spine switches are aggregate Layer 3 switches that provide high-bandwidth connectivity between leaf switches. Spine switches are also fully programmable and support all Layer 2 and Layer 3 protocols.
Cisco ACI is a software-defined networking (SDN) technology that enables virtualization of the network infrastructure. Cisco ACI offers a number of benefits, including improved agility, reduced complexity, and enhanced security.
Cisco ACI provides numerous benefits that can help organizations improve their agility, reduce complexity, and enhance security. When considering an SDN solution, Cisco ACI should be high on the list of choices.
Cisco ACI enables network administrators to centrally manage and orchestrate network resources through a graphical user interface (GUI). Cisco ACI can be used for a variety of purposes, including the following:
Cisco ACI integrates with other products using a variety of methods to provide customers with the ability to create a best-of-breed solution.
Cisco ACI provides customers with the ability to create a best-of-breed solution by integrating with other products using open APIs, jointly certified solutions, and service chaining. This advantage gives customers the flexibility to choose the products that best meet their needs while still taking advantage of Cisco ACI’s industry-leading features and performance.
With the release of Cisco ACI, the company is looking to solidify its position as a market leader in data center networking. While SDN has been around for a few years now, ACI represents a more holistic and comprehensive approach to SDN that takes into account all aspects of networking. So, ACI is an important tool for companies looking to move to the cloud or build out their data center infrastructure. If you’re curious about how Cisco ACI can benefit your business, reach out and we’ll be happy to discuss it with you.

Red Hat Enterprise Linux (RHEL) 9.3 is a major release of the enterprise Linux operating system from Red Hat, which was released on November 8, 2023 and comes with a number of new features and enhancements.
RHEL 9.3 is a third release in the Red Hat family since the acquisition of Red Hat by IBM in July 2019, and the third major version since the deprecation of the CentOS Project in favor of CentOS Stream which is now the upstream of RHEL.
RHEL 9.3 is the latest major version of RHEL and comes with Kernel 5.14 and a host of new software packages and tons of enhancements. It places an emphasis on security, stability, flexibility, and reliability.
Key Highlights of RHEL 9.3
At a glance, here are the major highlights of RHEL 9.3.
New Software Versions
RHEL 9.3 ships with new versions of software including Python 3.11. Node.JS 18, GCC 12, Perl 5.36, Ruby 3.1, PHP 8.2, and many more.
The Red Hat Developer Subscription is a no-cost offering of the Red Hat Developer program that is tailored for individual developers who want to reap the full benefits of Red Hat Enterprise Linux.
It gives developers access to all versions of Red Hat Enterprise Linux among other Red Hat products such as add-ons, software updates, and security errata.
Before anything else, make sure that you have an active Red Hat account. If you don’t have an account yet, navigate to the Red Hat Customer Portal and click on the ‘Register’ button and fill in your details to create a Red Hat account.
Once you have created a Red Hat account, you are all set to start downloading RHEL 9.3. To download Red Hat Enterprise Linux 9.3 at absolutely no cost, head over to the Red Hat Developer Portal and sign in using your account credentials.
Next, navigate to the RHEL 9.3 download page and click on the download button shown below.
Shortly after, the download of the RHEL 9.3 ISO image will begin. You should see a confirmation message informing you that the download of the RHEL 9 is underway.
The download size of the ISO image is about 8GB. As such, ensure that you have a high-speed internet connection for a faster download.
With the ISO image downloaded, grab a 16 GB USB drive and create a bootable USB drive using application such as UnetBootIn or dd command to make it bootable.
With your bootable medium at hand, plug it into the PC that you wish to install RHEL 9.3 on and reboot the system. Remember to configure the BIOS to have the bootable medium first in the boot priority so that the system boots into the medium first.
Also, ensure that you have a high-speed internet connection that will come in handy during the installation.
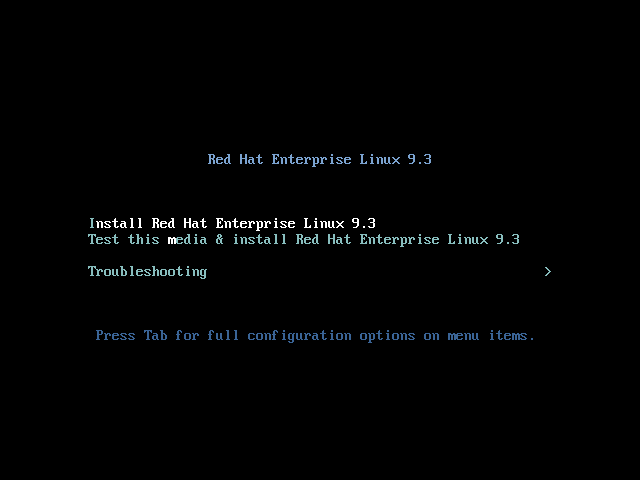
When the system reboots, you will get a black screen with the following options. To begin the installation, press ENTER on the first option ‘Install Red Hat Enterprise Linux 9.3’.
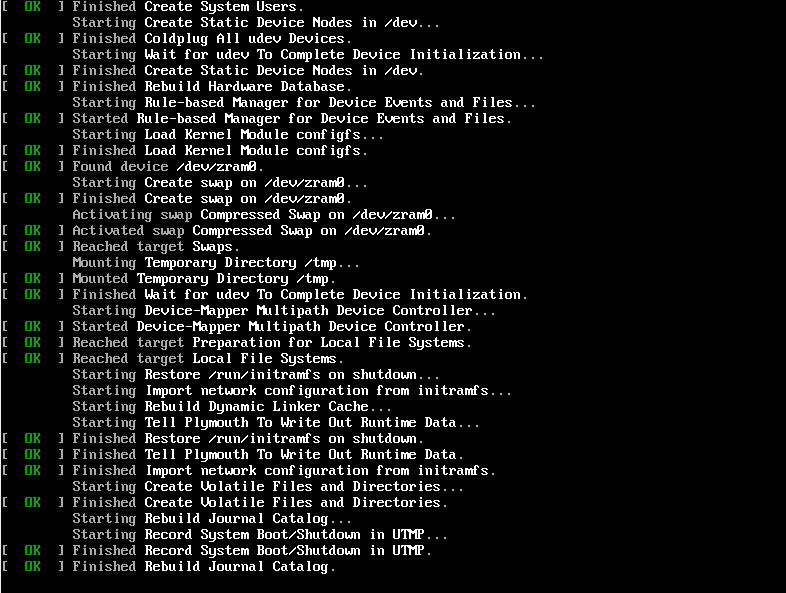
Shortly afterward, the following boot messages will be splashed on the screen. No action will be required so, just patiently wait as the installer gets ready to install RHEL.
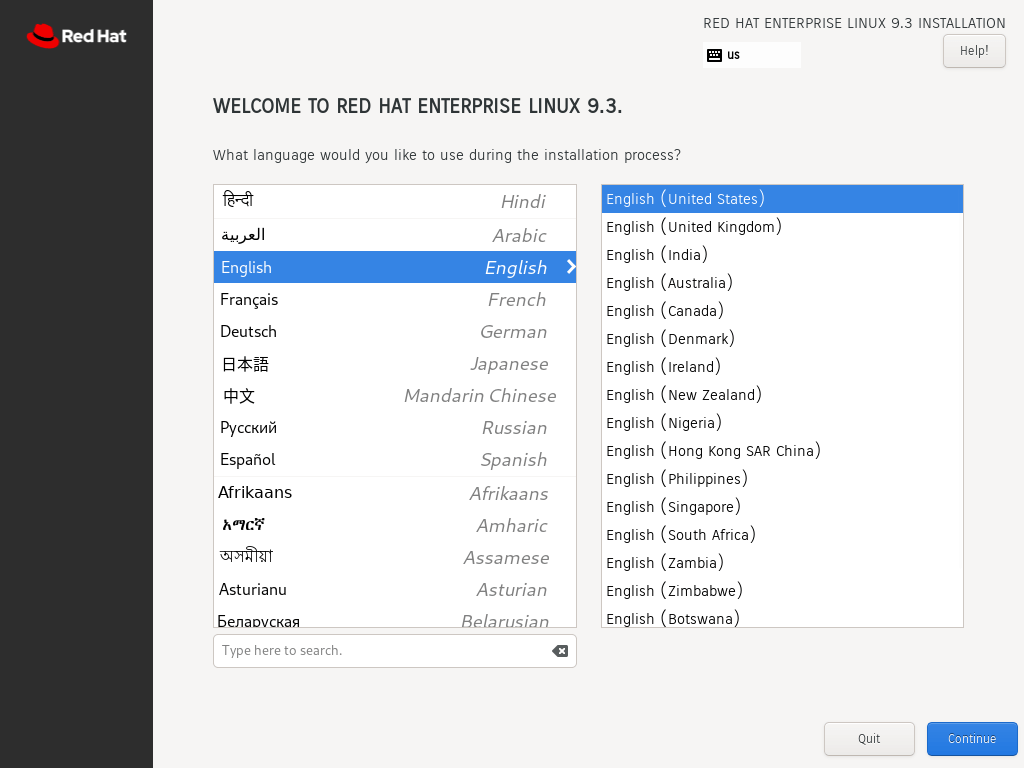
After a few seconds, the graphical wizard for installing Red Hat Enterprise Linux 9.3. In the first step, select your preferred language and click ‘Continue’.
The next step presents you with an installation summary that is segmented into four sections:
We will only focus on three items that are mandatory before proceeding with the installation – Installation Destination, Root Account, and Regular Account creation.
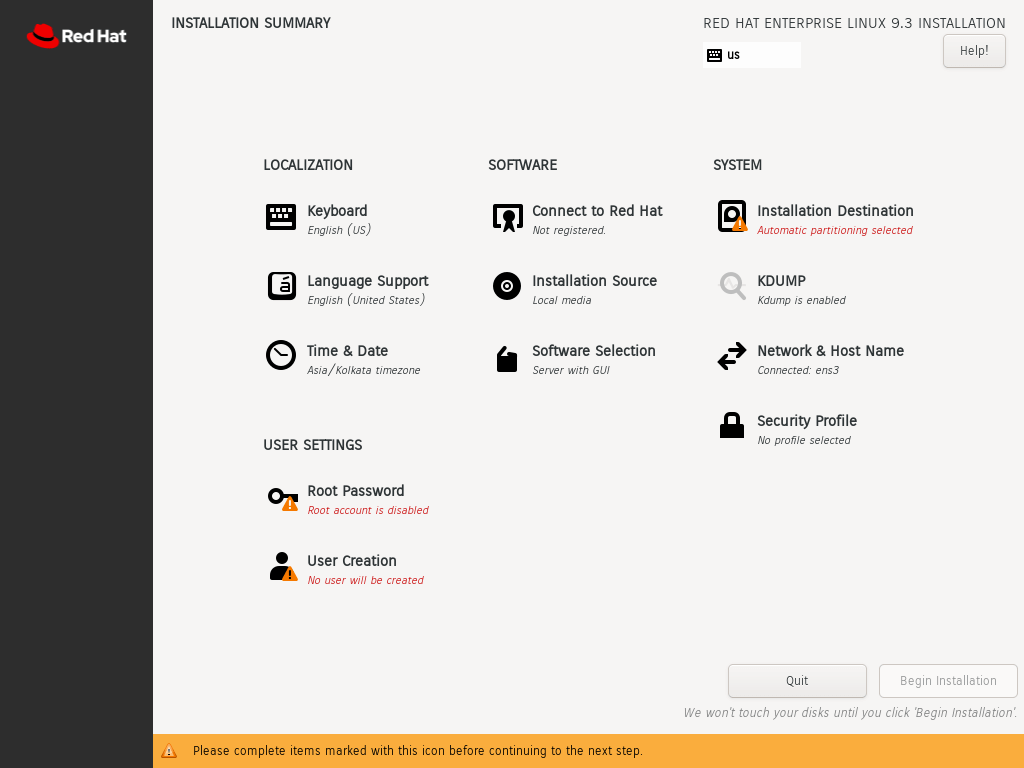
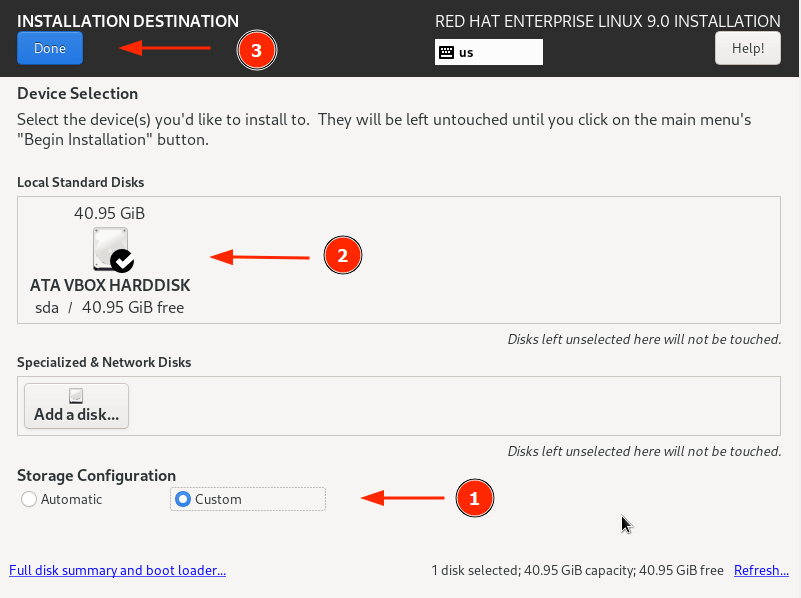
To set up partitioning, click on ‘Installation Destination’ under SYSTEM. On the ‘Installation Destination’ page, ensure that you have selected the ‘Automatic’ option if you wish the wizard to automatically partition the hard drive. Otherwise, select ‘Custom’ to manually create the partitions.
In addition, ensure that you have selected the hard disk on your PC. Then click ‘Done’.
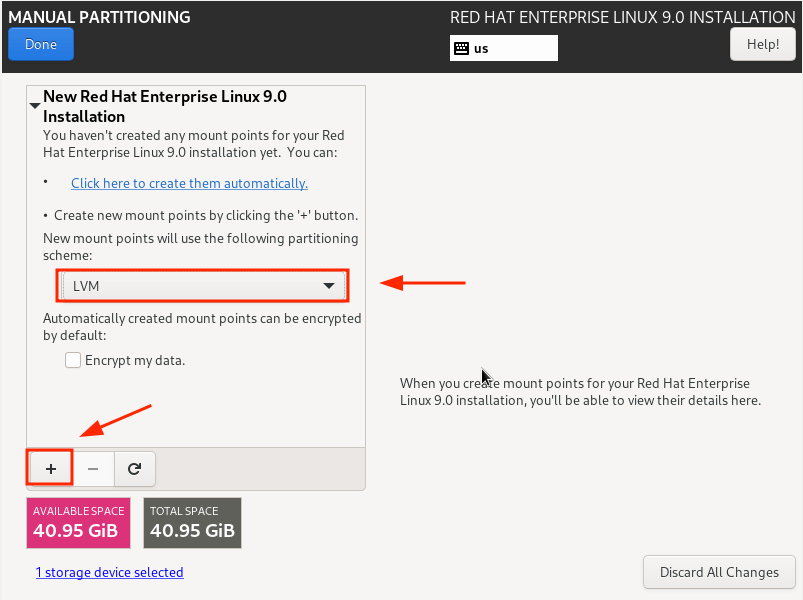
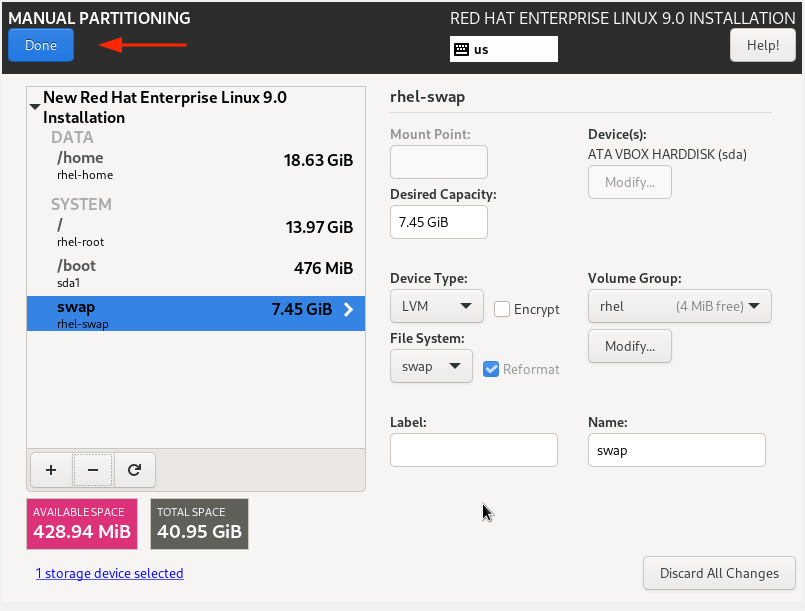
This takes you to the ‘Manual Partitioning’ window. By default, the LVM partitioning scheme is selected, which is just fine.
To start creating the partitions, click on the plus [ + ] sign.
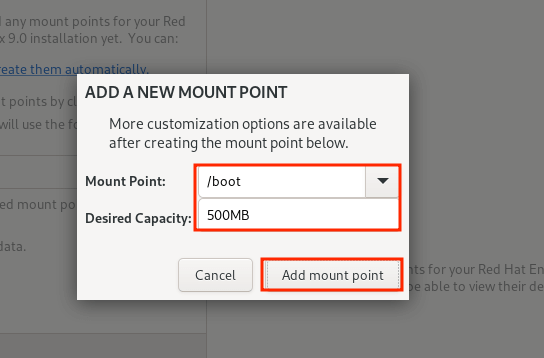
For demonstration purposes, we will create the following partitions./boot – 500MB /home – 20GB /root – 15GB swap – 8GB
First, we will specify the boot option.
From the partition table below, you can see that the boot partition has been created.
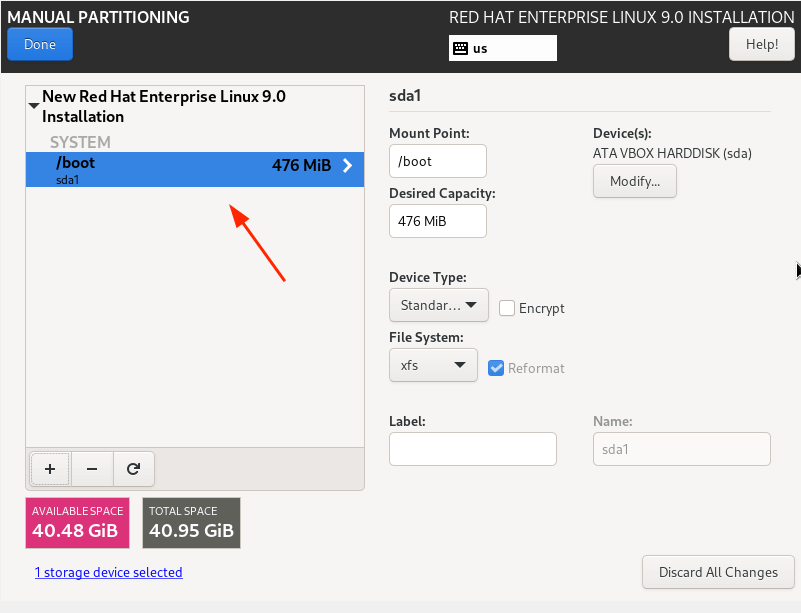
Repeat the same steps and create the /home, /root, and swap mount points.
Our complete partition table is shown below. To save the changes, click on ‘Done’.
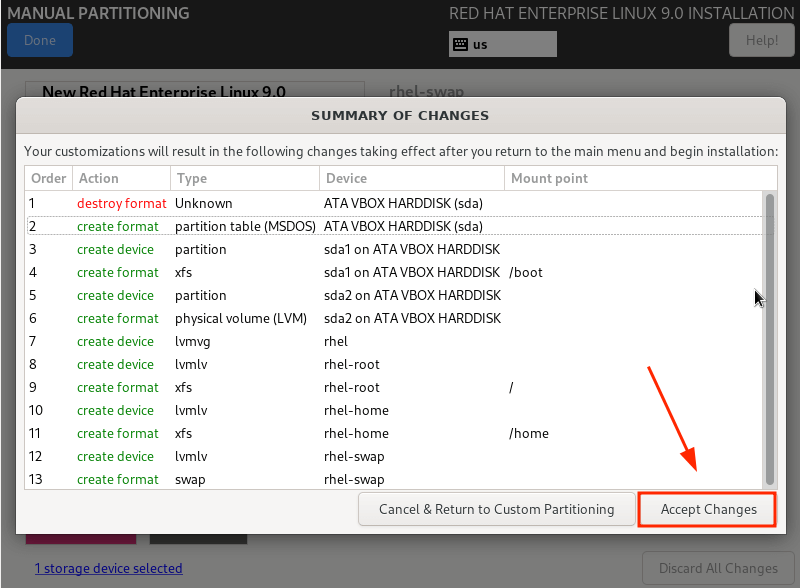
Then click ‘Accept Changes’ on the pop-up that appears.
Next, we are going to configure user settings, starting off with the Root password. So, click on the ‘Root Password’ icon.
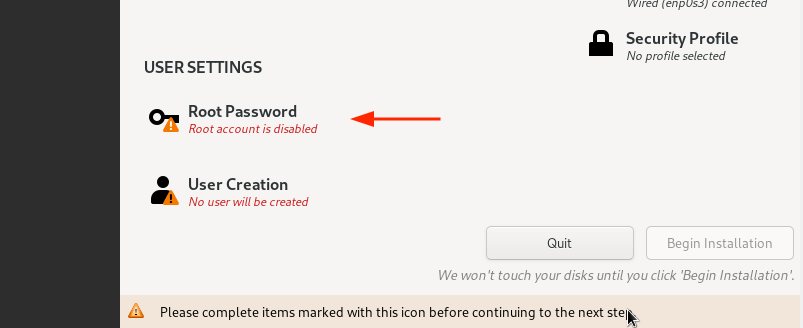
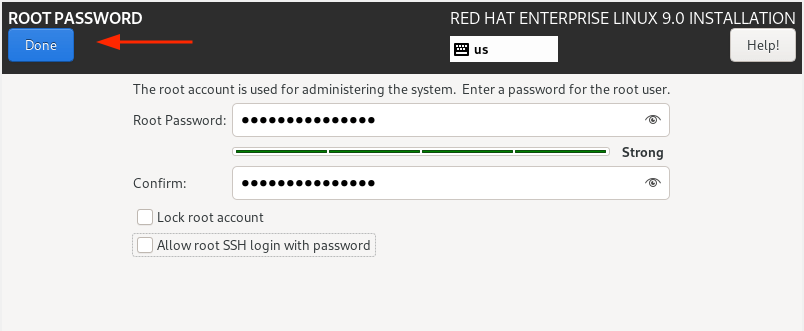
Unlock the Root account by providing a root password and confirming it. Then click ‘Done’.
Next, create a regular login user by clicking on ‘User creation’.
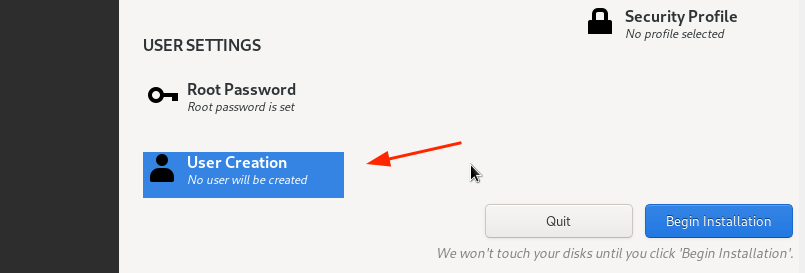
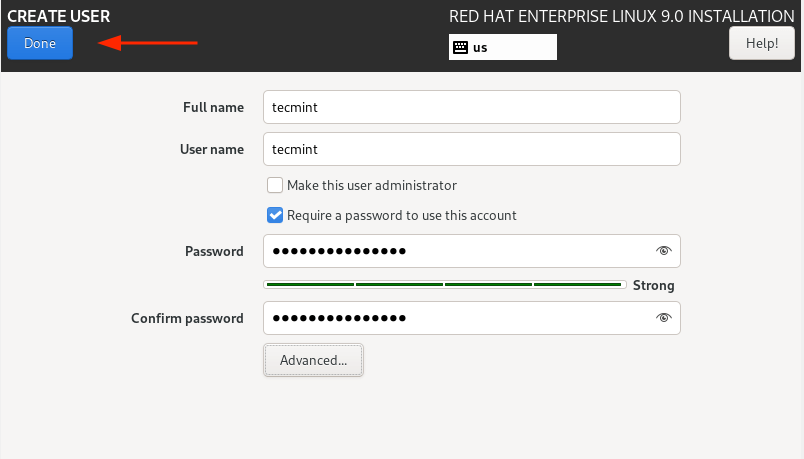
Provide the username and password details of the user and click ‘Done’.
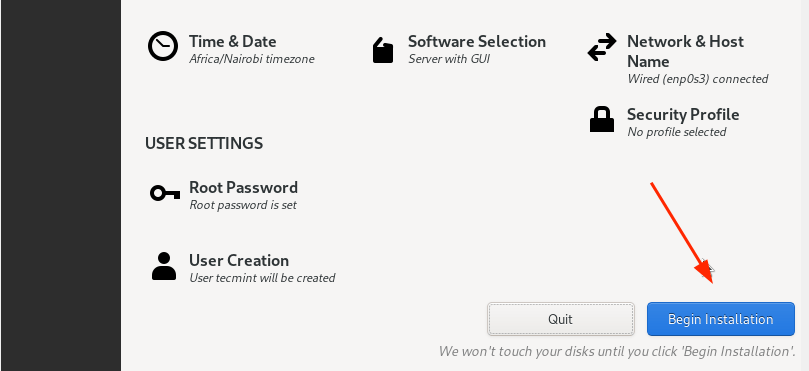
We are now all set to proceed with the installation. So, click on ‘Begin Installation’.
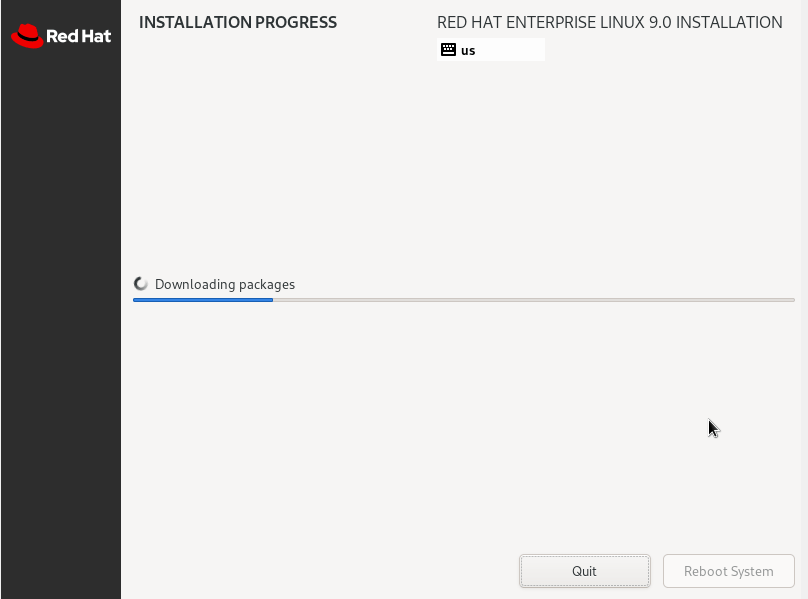
The Wizard will download all the required packages from the RedHat ISO image and save them to the hard drive. This is a process that takes quite a bit of time, and this is an ideal moment to take a break as the installation progresses.
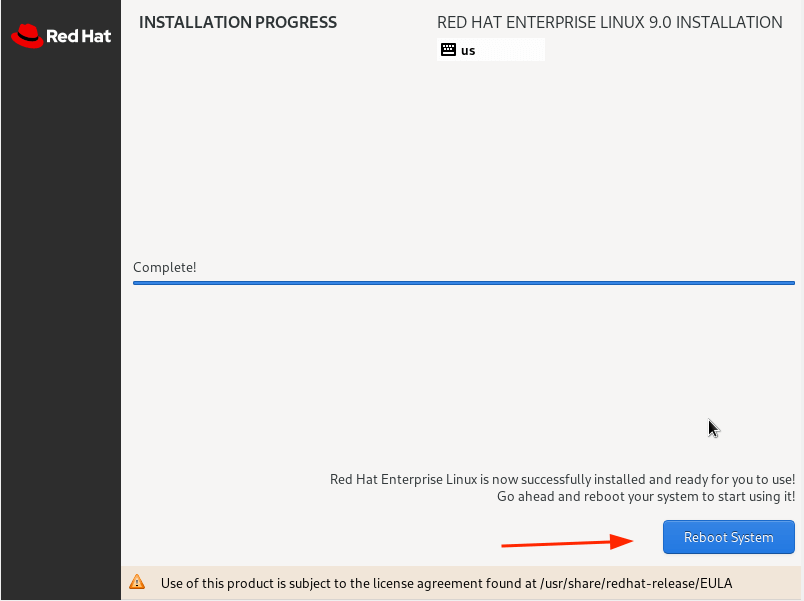
Once the installation is complete, you will be required to reboot your system so that you can log in to your fresh RHEL 9 installation.
So, click the ‘Reboot System’ button.
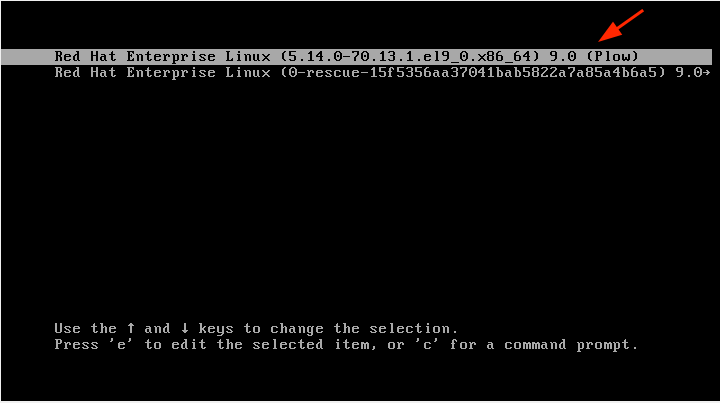
Once the system reboots, select the first entry on the GRUB menu that points to Red Hat Enterprise Linux 9.0.
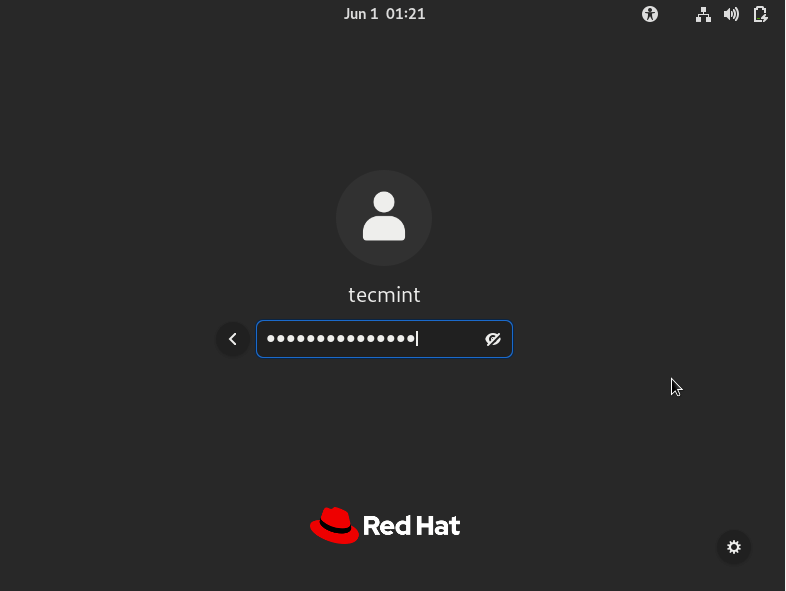
Shortly afterward, provide your password on the login screen and press ENTER.
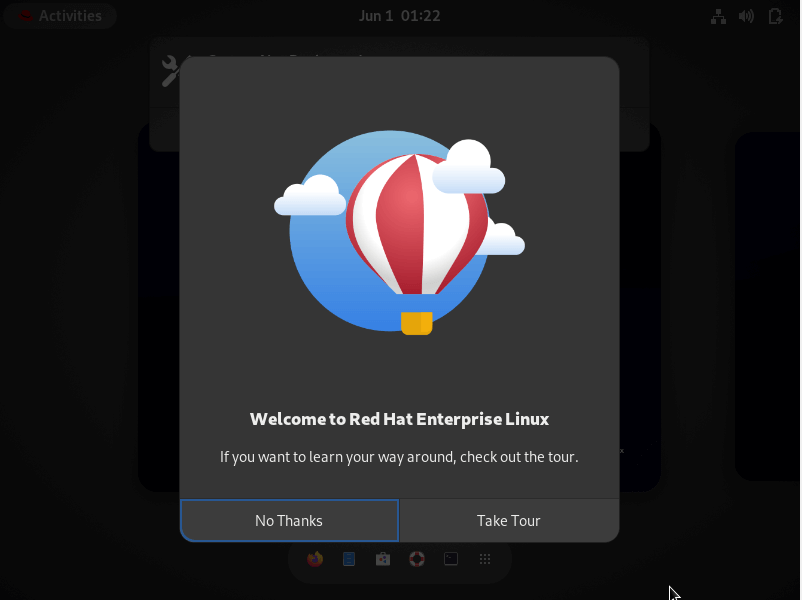
Once logged in, you can opt to take a tour of the freshly installed RHEL 9 or decline and go straight to the Desktop.
Finally, you will see the GNOME 42 desktop environment which has received a facelift and looks quite elegant.
Introduction
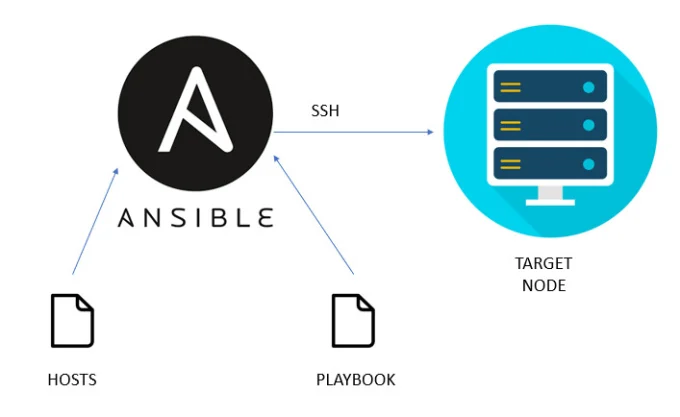
Ansible is a very powerful open-source IT automation tool. It is known as a configuration management tool. Ansible is written in Python language, so it requires Python to be available on the machine. We can use Ansible to automate software installation, software configuration, configuration management, etc.
To get a quick high-level understanding of Ansible, please review the article below.
To use Ansible for your automation purpose you would need a machine where Ansible needs to be installed and this is called ansible-host or ansible-controller. And you would need other machines (remote or target machines) where Ansible will perform the tasks.
There are multiple ways to install Ansible in RHEL. Below are the two most used methods.
Ansible installation using RHEL package manager.
Ansible installation using the pip module of Python.
In this article, we will see how to install Ansible using the RHEL package manager in a step-by-step manner.


As of April 2023, the latest version of Ansible is 2.13.x (ansible core). We will be installing the same.
We will be using dnf to install Ansible. (dnf is the package management utility for RHEL, Fedora, and Centos).
# Run the below command to update the RHEL OS.
sudo dnf update -y
# Check whether Python is installed or not. RHEL 8 comes with python3. So, we don’t need to install Python.python3 -V
# If Python is not installed, then run the below command to install it.
sudo dnf install python3
# List the available repos that include ansible-core packages
sudo dnf list ansible-core
OR
sudo dnf info ansible-core
In the output of the above, we will see the repo name. We need to enable that repo.
# Enable the repo that includes the ansible-core package.
sudo subscription-manager repos –enable <repo name>
# Run the below commands to install Ansible
sudo dnf install ansible -y
# Finally, we can check the version of Ansible.
ansible –version
Apart from the above method of Ansible installation, we can install Ansible by following the official documentation of Ansible
https://docs.ansible.com/ansible/latest/installation_guide/intro_installation.html

I am available for freelance work. Connect with me via and call in to my account.
Phone: +01234567890 Email: [email protected]